Cybersecurity for Business: Organization-Wide Strategies to Ensure Cyber Risk Is Not Just an IT Issue: Clinton, Larry: 9781398606388: Amazon.com: Books
Measuring Information Security Performance with 10 by 10 Model for Holistic State Evaluation | PLOS ONE

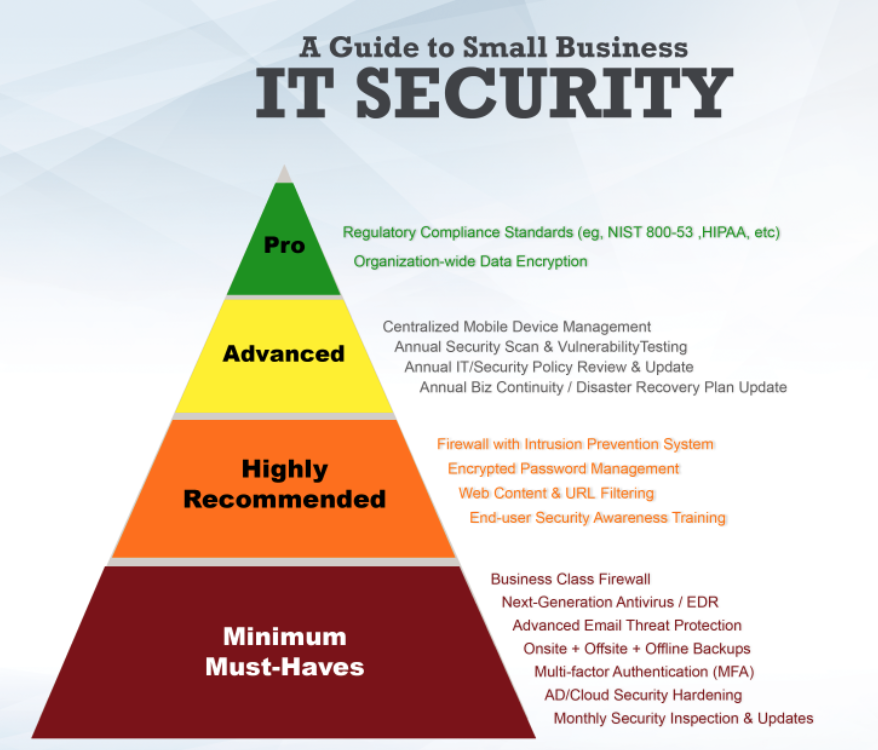
4 Business Network Security Must Haves for Small to Medium Organizations | by Munawar Abadullah | Medium
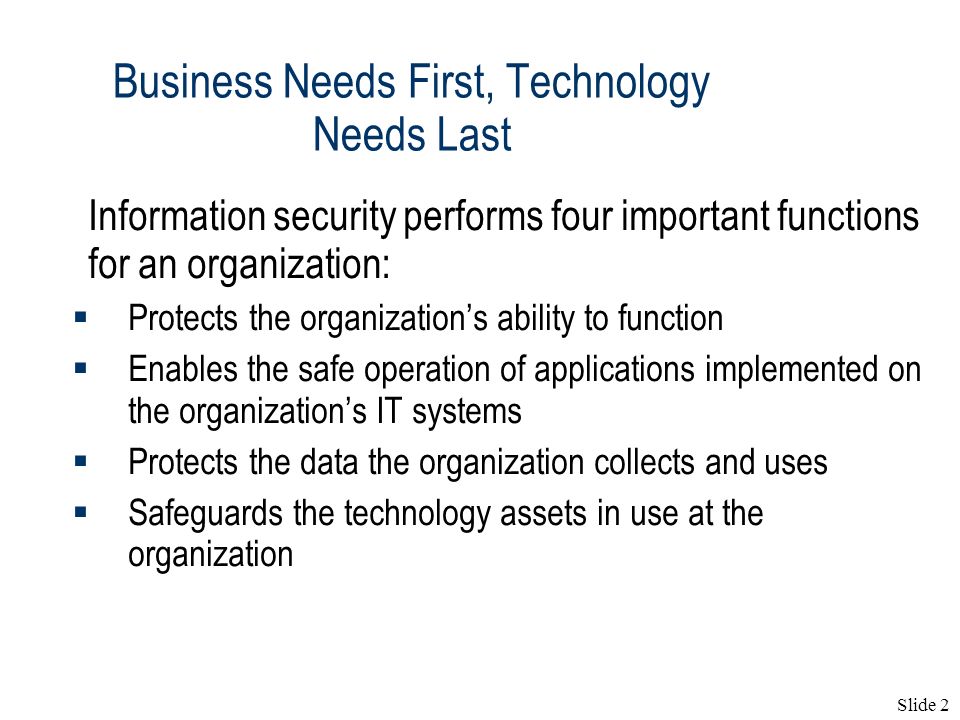
The Need for Information Security(1) Lecture 2. Slide 2 Business Needs First, Technology Needs Last Information security performs four important functions. - ppt download

New ICC cyber security guide outlines practical steps for business - ICC - International Chamber of Commerce